Cisco Secure Access
Cloud-delivered SSE platform with ZTNA, SWG, CASB, and DLP for securing hybrid workforces from a single console.

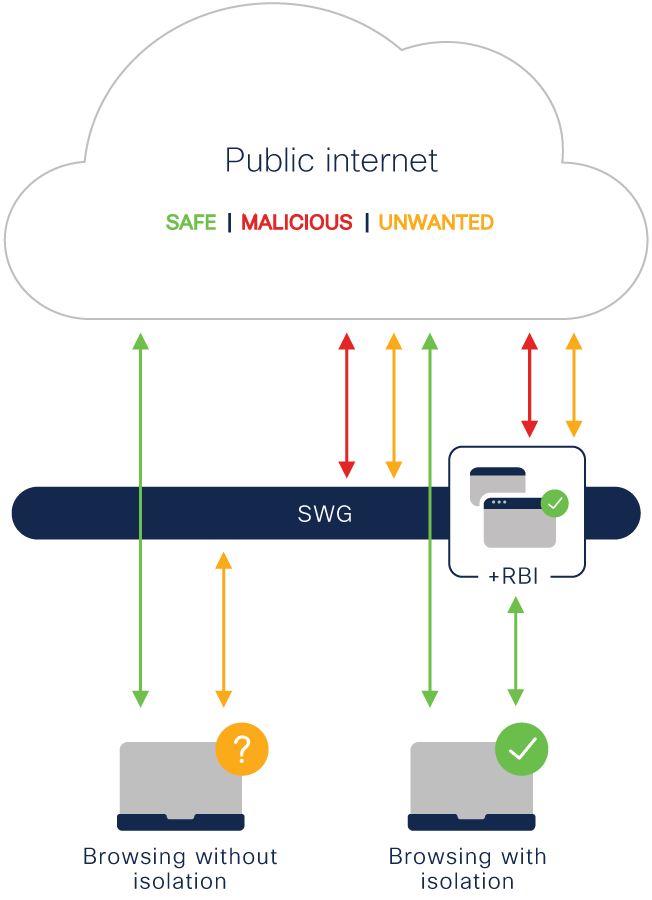
Cisco Umbrella Remote Browser Isolation
Cisco Umbrella Remote Browser Isolation executes all web content in a secure cloud environment, sending only a safe visual stream to the user’s browser. Malware, exploits, and ransomware never reach the endpoint — even from the most dangerous corners of the internet.
“Organizations that isolate internet web browsing will experience a 70% reduction in attacks that compromise end user systems.”
Malicious code embedded in web pages or advertising networks cannot execute on the endpoint. The isolated container absorbs the attack and is discarded after the session ends.
Unknown exploits targeting browser vulnerabilities have no path to the endpoint when browsing happens in an isolated cloud environment. Zero-day threats are contained in the remote container.
Legitimate websites that have been compromised by attackers can serve malware without warning. RBI protects users even on trusted sites that have been temporarily infected or hijacked.
Attacks that use JavaScript, Flash, or other active web technologies to exploit browser engines or plugins are stopped cold when those technologies execute only inside the isolated cloud container.
Browser-based cryptomining scripts hijack CPU resources to mine cryptocurrency without user consent. RBI ensures these scripts execute only inside the isolated container, never consuming endpoint resources.
Fileless malware exploits browser processes and scripting engines to execute entirely in memory, evading traditional file-based detection. RBI contains all script execution in the cloud, blocking fileless attacks at the source.
Targeted Protection
RBI is not designed to isolate all browsing — that would create unnecessary overhead for routine activity. Instead, it applies selectively to the scenarios where the risk of compromise is highest and the cost of blocking is unacceptable.
Apply RBI selectively using Umbrella’s policy engine — trigger isolation based on URL category, domain reputation score, user group, or a combination of conditions.
Users continue to browse normally. There is no visible indication that a session is isolated unless you configure a visual indicator — reducing friction and help desk calls. Works with all devices, browsers, and operating systems — no plugins or extensions required.
Configure whether users can download files from isolated sessions. You can allow downloads with automatic malware scanning, require read-only access, or block downloads entirely for specific site categories.
The Next Evolution
Our Cisco-certified team will help you deploy Umbrella Remote Browser Isolation, configure policies for your highest-risk user groups and URL categories, and integrate RBI with your existing Umbrella deployment.