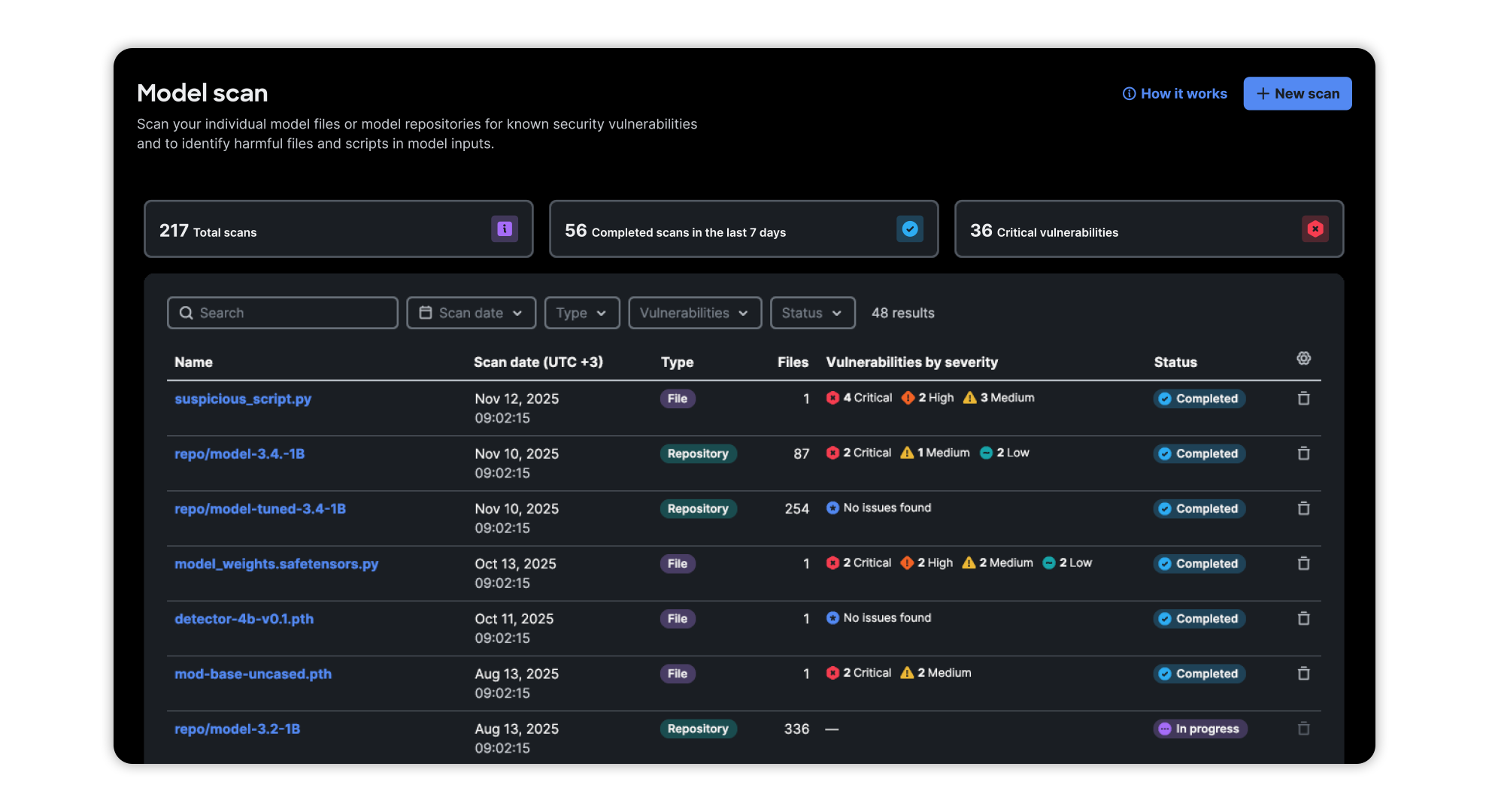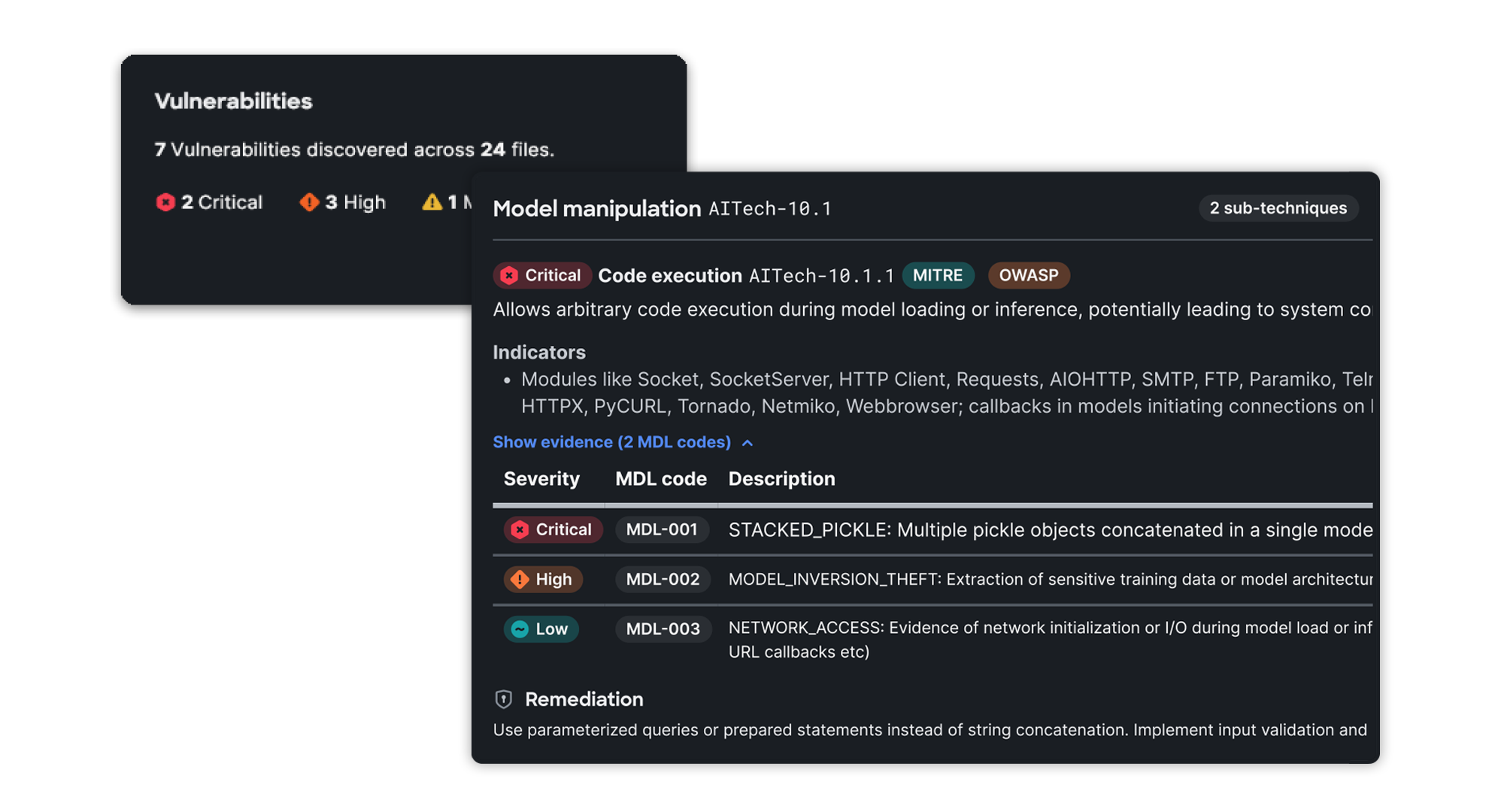
Scan Open-Source Models
Millions of open-source models are available online, offering AI developers a multitude of options. Nevertheless, developers must be wary of malicious behaviors, model backdoors, and other potential vulnerabilities. AI Defense scans models in your registry to identify and flag these risks before you build on a compromised foundation.